#include <curl/curl.h>#include <sys/stat.h>#include <jwt.h>#include <regex.h>#include "asterisk.h"#include "asterisk/channel.h"#include "asterisk/cli.h"#include "asterisk/config.h"#include "asterisk/module.h"#include "asterisk/sorcery.h"#include "asterisk/astdb.h"#include "asterisk/conversions.h"#include "asterisk/utils.h"#include "asterisk/paths.h"#include "asterisk/logger.h"#include "asterisk/acl.h"#include "asterisk/time.h"#include "asterisk/localtime.h"#include "asterisk/crypto.h"#include "asterisk/json.h"#include "stir_shaken.h"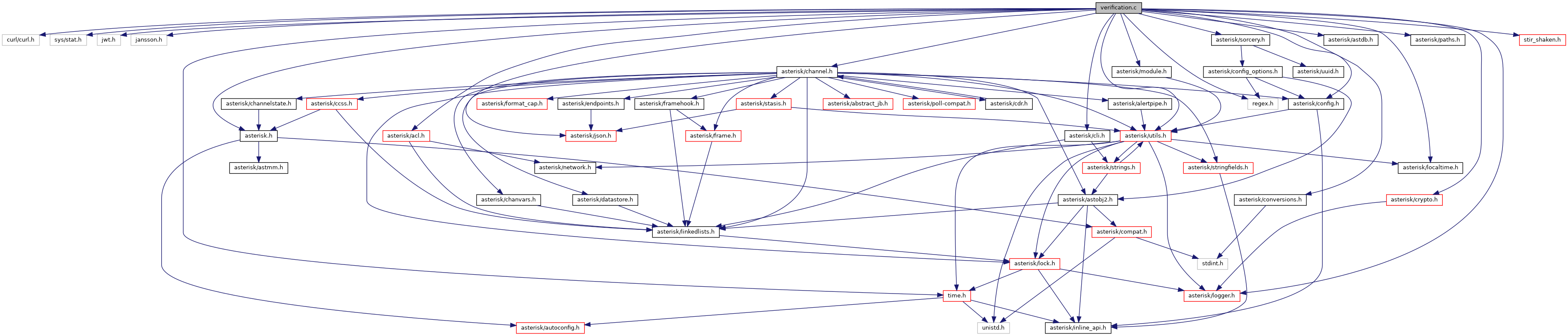
Go to the source code of this file.
Macros | |
| #define | _TRACE_PREFIX_ "v",__LINE__, "" |
| #define | ASN1_TAG_TNAUTH_SPC 0 |
| #define | ASN1_TAG_TNAUTH_TN 2 |
| #define | ASN1_TAG_TNAUTH_TN_RANGE 1 |
| #define | AST_DB_FAMILY "STIR_SHAKEN" |
| #define | BEGIN_CERTIFICATE_STR "-----BEGIN CERTIFICATE-----" |
| #define | DUMP_X5U_MATCH() |
| #define | FULL_URL_REGEX "^([a-zA-Z]+)://(([^@]+@[^:]+):)?(([^:/?]+)|([0-9.]+)|([[][0-9a-fA-F:]+[]]))(:([0-9]+))?(/([^#\\?]+))?(\\?([^#]+))?(#(.*))?" |
| #define | FULL_URL_REGEX_GROUPS 15 |
| #define | get_match_string(__x5u, __pmatch, __i) |
| #define | IS_GET_OBJ_ERR(ret) (ret & 0x80) |
| #define | URL_MATCH_FRAGMENT 15 |
| #define | URL_MATCH_HOST 4 |
| #define | URL_MATCH_PATH 11 |
| #define | URL_MATCH_PORT 9 |
| #define | URL_MATCH_QUERY 13 |
| #define | URL_MATCH_SCHEME 1 |
| #define | URL_MATCH_USERPASS 3 |
Variables | |
| static regex_t | url_match_regex |
| static const char * | vs_rc_map [] |
Macro Definition Documentation
◆ _TRACE_PREFIX_
| #define _TRACE_PREFIX_ "v",__LINE__, "" |
Definition at line 26 of file verification.c.
◆ ASN1_TAG_TNAUTH_SPC
| #define ASN1_TAG_TNAUTH_SPC 0 |
Definition at line 247 of file verification.c.
◆ ASN1_TAG_TNAUTH_TN
| #define ASN1_TAG_TNAUTH_TN 2 |
Definition at line 249 of file verification.c.
◆ ASN1_TAG_TNAUTH_TN_RANGE
| #define ASN1_TAG_TNAUTH_TN_RANGE 1 |
Definition at line 248 of file verification.c.
◆ AST_DB_FAMILY
| #define AST_DB_FAMILY "STIR_SHAKEN" |
Definition at line 46 of file verification.c.
◆ BEGIN_CERTIFICATE_STR
| #define BEGIN_CERTIFICATE_STR "-----BEGIN CERTIFICATE-----" |
Definition at line 51 of file verification.c.
◆ DUMP_X5U_MATCH
| #define DUMP_X5U_MATCH | ( | ) |
Definition at line 823 of file verification.c.
◆ FULL_URL_REGEX
| #define FULL_URL_REGEX "^([a-zA-Z]+)://(([^@]+@[^:]+):)?(([^:/?]+)|([0-9.]+)|([[][0-9a-fA-F:]+[]]))(:([0-9]+))?(/([^#\\?]+))?(\\?([^#]+))?(#(.*))?" |
Definition at line 784 of file verification.c.
◆ FULL_URL_REGEX_GROUPS
| #define FULL_URL_REGEX_GROUPS 15 |
Definition at line 785 of file verification.c.
◆ get_match_string
| #define get_match_string | ( | __x5u, | |
| __pmatch, | |||
| __i | |||
| ) |
Definition at line 811 of file verification.c.
◆ IS_GET_OBJ_ERR
| #define IS_GET_OBJ_ERR | ( | ret | ) | (ret & 0x80) |
Definition at line 251 of file verification.c.
◆ URL_MATCH_FRAGMENT
| #define URL_MATCH_FRAGMENT 15 |
Definition at line 809 of file verification.c.
◆ URL_MATCH_HOST
| #define URL_MATCH_HOST 4 |
Definition at line 805 of file verification.c.
◆ URL_MATCH_PATH
| #define URL_MATCH_PATH 11 |
Definition at line 807 of file verification.c.
◆ URL_MATCH_PORT
| #define URL_MATCH_PORT 9 |
Definition at line 806 of file verification.c.
◆ URL_MATCH_QUERY
| #define URL_MATCH_QUERY 13 |
Definition at line 808 of file verification.c.
◆ URL_MATCH_SCHEME
| #define URL_MATCH_SCHEME 1 |
Definition at line 803 of file verification.c.
◆ URL_MATCH_USERPASS
| #define URL_MATCH_USERPASS 3 |
Definition at line 804 of file verification.c.
Function Documentation
◆ add_cert_expiration_to_astdb()
|
static |
Definition at line 112 of file verification.c.
References ao2_cleanup, ast_db_put(), ast_mktime(), ast_str_to_uint(), ast_strlen_zero(), ast_strptime(), crypto_asn_time_as_time_t(), ast_stir_shaken_vs_ctx::expiration, ast_stir_shaken_vs_ctx::hash_family, NULL, RAII_VAR, ast_tm::tm_isdst, vs_get_cfg(), and ast_stir_shaken_vs_ctx::xcert.
Referenced by add_cert_key_to_astdb().
◆ add_cert_key_to_astdb()
|
static |
Definition at line 201 of file verification.c.
References add_cert_expiration_to_astdb(), ast_db_del(), ast_db_put(), ast_stir_shaken_vs_ctx::filename, ast_stir_shaken_vs_ctx::hash, ast_stir_shaken_vs_ctx::hash_family, ast_stir_shaken_vs_ctx::public_url, and ast_stir_shaken_vs_ctx::url_family.
Referenced by retrieve_cert_from_url().
◆ ast_stir_shaken_vs_ctx_add_date_hdr()
| enum ast_stir_shaken_vs_response_code ast_stir_shaken_vs_ctx_add_date_hdr | ( | struct ast_stir_shaken_vs_ctx * | ctx, |
| const char * | date_hdr | ||
| ) |
Add the received Date header value to the VS context.
- Parameters
-
ctx VS context date_hdr Date header value
- Return values
-
AST_STIR_SHAKEN_VS_SUCCESS if successful Other AST_STIR_SHAKEN_VS errors.
Definition at line 614 of file verification.c.
References AST_STIR_SHAKEN_VS_INTERNAL_ERROR, AST_STIR_SHAKEN_VS_SUCCESS, and ast_string_field_set.
Referenced by stir_shaken_incoming_request().
◆ ast_stir_shaken_vs_ctx_add_identity_hdr()
| enum ast_stir_shaken_vs_response_code ast_stir_shaken_vs_ctx_add_identity_hdr | ( | struct ast_stir_shaken_vs_ctx * | ctx, |
| const char * | identity_hdr | ||
| ) |
Add the received Identity header value to the VS context.
- Parameters
-
ctx VS context identity_hdr Identity header value
- Return values
-
AST_STIR_SHAKEN_VS_SUCCESS if successful Other AST_STIR_SHAKEN_VS errors.
Definition at line 606 of file verification.c.
References AST_STIR_SHAKEN_VS_INTERNAL_ERROR, AST_STIR_SHAKEN_VS_SUCCESS, and ast_string_field_set.
Referenced by stir_shaken_incoming_request().
◆ ast_stir_shaken_vs_ctx_create()
| enum ast_stir_shaken_vs_response_code ast_stir_shaken_vs_ctx_create | ( | const char * | caller_id, |
| struct ast_channel * | chan, | ||
| const char * | profile_name, | ||
| const char * | tag, | ||
| struct ast_stir_shaken_vs_ctx ** | ctxout | ||
| ) |
Create Verification Service context.
- Parameters
-
caller_id Incoming caller id chan Incoming channel profile_name The profile name on the endpoint May be NULL. endpoint_behavior Behavior associated to the specific endpoint tag Identifying string to output in log and trace messages. ctxout Receives a pointer to the newly created context The caller must release with ao2_ref or ao2_cleanup.
- Return values
-
AST_STIR_SHAKEN_VS_SUCCESS if successful. AST_STIR_SHAKEN_VS_DISABLED if verification is disabled by the endpoint itself, the profile or globally. Other AST_STIR_SHAKEN_VS errors.
Definition at line 659 of file verification.c.
References AO2_ALLOC_OPT_LOCK_NOLOCK, ao2_alloc_options, ao2_cleanup, ao2_ref, ast_channel_name(), ast_free, AST_STIR_SHAKEN_VS_DISABLED, AST_STIR_SHAKEN_VS_INTERNAL_ERROR, AST_STIR_SHAKEN_VS_INVALID_ARGUMENTS, AST_STIR_SHAKEN_VS_SUCCESS, ast_string_field_init, ast_string_field_set, ast_strlen_zero(), ast_stir_shaken_vs_ctx::caller_id, canonicalize_tn_alloc(), ast_stir_shaken_vs_ctx::chan, ctx_destructor(), eprofile_get_cfg(), LOG_ERROR, NULL, PROFILE_ALLOW_VERIFY, RAII_VAR, S_COR, S_OR, SCOPE_ENTER, SCOPE_EXIT_LOG_RTN_VALUE, SCOPE_EXIT_RTN_VALUE, ast_stir_shaken_vs_ctx::tag, and vs_get_cfg().
Referenced by stir_shaken_incoming_request().
◆ ast_stir_shaken_vs_ctx_set_response_code()
| void ast_stir_shaken_vs_ctx_set_response_code | ( | struct ast_stir_shaken_vs_ctx * | ctx, |
| enum ast_stir_shaken_vs_response_code | vs_rc | ||
| ) |
Sets response code on VS context.
- Parameters
-
ctx VS context vs_rc ast_stir_shaken_vs_response_code to set
Definition at line 640 of file verification.c.
References ast_stir_shaken_vs_ctx::failure_reason.
Referenced by process_failure().
◆ ast_stir_shaken_vs_get_caller_id()
| const char * ast_stir_shaken_vs_get_caller_id | ( | struct ast_stir_shaken_vs_ctx * | ctx | ) |
Get caller_id from context.
- Parameters
-
ctx VS context
- Return values
-
Caller ID or NULL
Definition at line 634 of file verification.c.
References ast_stir_shaken_vs_ctx::caller_id.
Referenced by stir_shaken_incoming_request().
◆ ast_stir_shaken_vs_get_failure_action()
| enum stir_shaken_failure_action_enum ast_stir_shaken_vs_get_failure_action | ( | struct ast_stir_shaken_vs_ctx * | ctx | ) |
Get failure_action from context.
- Parameters
-
ctx VS context
- Return values
-
ast_stir_shaken_failure_action
Definition at line 622 of file verification.c.
References ast_stir_shaken_vs_ctx::eprofile, verification_cfg_common::stir_shaken_failure_action, and profile_cfg::vcfg_common.
Referenced by process_failure().
◆ ast_stir_shaken_vs_get_use_rfc9410_responses()
| int ast_stir_shaken_vs_get_use_rfc9410_responses | ( | struct ast_stir_shaken_vs_ctx * | ctx | ) |
Get use_rfc9410_responses from context.
- Parameters
-
ctx VS context
- Return values
-
1 if true 0 if false
Definition at line 628 of file verification.c.
References ast_stir_shaken_vs_ctx::eprofile, verification_cfg_common::use_rfc9410_responses, and profile_cfg::vcfg_common.
Referenced by process_failure().
◆ ast_stir_shaken_vs_verify()
| enum ast_stir_shaken_vs_response_code ast_stir_shaken_vs_verify | ( | struct ast_stir_shaken_vs_ctx * | ctx | ) |
Perform incoming call verification.
- Parameters
-
ctx VS context
- Return values
-
AST_STIR_SHAKEN_AS_SUCCESS if successful Other AST_STIR_SHAKEN_AS errors.
Definition at line 895 of file verification.c.
References ast_free, ast_json_dump_string, ast_json_free(), ast_json_load_string(), ast_json_object_get(), ast_json_object_string_get, ast_json_unref(), ast_malloc, ast_std_free(), AST_STIR_SHAKEN_VS_CID_ORIG_TN_MISMATCH, AST_STIR_SHAKEN_VS_IAT_EXPIRED, AST_STIR_SHAKEN_VS_INTERNAL_ERROR, AST_STIR_SHAKEN_VS_INVALID_HEADER, AST_STIR_SHAKEN_VS_INVALID_OR_NO_ALG, AST_STIR_SHAKEN_VS_INVALID_OR_NO_ATTEST, AST_STIR_SHAKEN_VS_INVALID_OR_NO_GRANTS, AST_STIR_SHAKEN_VS_INVALID_OR_NO_PPT, AST_STIR_SHAKEN_VS_INVALID_OR_NO_TYP, AST_STIR_SHAKEN_VS_INVALID_OR_NO_X5U, AST_STIR_SHAKEN_VS_NO_DEST_TN, AST_STIR_SHAKEN_VS_NO_IAT, AST_STIR_SHAKEN_VS_NO_ORIG_TN, AST_STIR_SHAKEN_VS_NO_ORIGID, AST_STIR_SHAKEN_VS_SIGNATURE_VALIDATION, AST_STIR_SHAKEN_VS_SUCCESS, ast_string_field_set, ast_strlen_zero(), ast_trace, ast_stir_shaken_vs_ctx::caller_id, check_date_header(), check_x5u_url(), ctx_populate(), ast_stir_shaken_vs_ctx::date_hdr_time, ast_stir_shaken_vs_ctx::eprofile, ast_stir_shaken_vs_ctx::identity_hdr, len(), LOG_ERROR, verification_cfg_common::max_iat_age, NULL, ast_stir_shaken_vs_ctx::orig_tn, ast_stir_shaken_vs_ctx::public_url, RAII_VAR, ast_stir_shaken_vs_ctx::raw_key, ast_stir_shaken_vs_ctx::raw_key_len, retrieve_verification_cert(), SCOPE_ENTER, SCOPE_EXIT_LOG_RTN_VALUE, SCOPE_EXIT_RTN_VALUE, STIR_SHAKEN_ENCRYPTION_ALGORITHM, STIR_SHAKEN_PPT, STIR_SHAKEN_TYPE, ast_stir_shaken_vs_ctx::tag, TRACE_ATLEAST, ast_stir_shaken_vs_ctx::validity_check_time, profile_cfg::vcfg_common, and vs_response_code_to_str().
Referenced by stir_shaken_incoming_request().
◆ check_cert()
|
static |
Definition at line 326 of file verification.c.
References ast_free, AST_STIR_SHAKEN_VS_CERT_CONTENTS_INVALID, AST_STIR_SHAKEN_VS_CERT_DATE_INVALID, AST_STIR_SHAKEN_VS_CERT_NOT_TRUSTED, AST_STIR_SHAKEN_VS_INTERNAL_ERROR, AST_STIR_SHAKEN_VS_NO_RAW_KEY, ast_string_field_set, ast_trace, ast_stir_shaken_vs_ctx::cert_cn, ast_stir_shaken_vs_ctx::cert_spc, check_tn_auth_list(), crypto_get_cert_subject(), crypto_get_raw_pubkey_from_cert(), crypto_is_cert_time_valid(), crypto_is_cert_trusted(), ast_stir_shaken_vs_ctx::eprofile, LOG_ERROR, NULL, ast_stir_shaken_vs_ctx::public_url, RAII_VAR, ast_stir_shaken_vs_ctx::raw_key, ast_stir_shaken_vs_ctx::raw_key_len, SCOPE_ENTER, SCOPE_EXIT_LOG_RTN_VALUE, SCOPE_EXIT_RTN_VALUE, ast_stir_shaken_vs_ctx::tag, verification_cfg_common::tcs, ast_stir_shaken_vs_ctx::validity_check_time, profile_cfg::vcfg_common, and ast_stir_shaken_vs_ctx::xcert.
Referenced by retrieve_cert_from_cache(), and retrieve_cert_from_url().
◆ check_date_header()
|
static |
Definition at line 726 of file verification.c.
References ast_mktime(), AST_STIR_SHAKEN_VS_DATE_HDR_EXPIRED, AST_STIR_SHAKEN_VS_DATE_HDR_PARSE_FAILURE, AST_STIR_SHAKEN_VS_NO_DATE_HDR, AST_STIR_SHAKEN_VS_SUCCESS, ast_strlen_zero(), ast_strptime(), ast_trace, ast_tvdiff_ms(), ast_tvnow(), ast_stir_shaken_vs_ctx::date_hdr, ast_stir_shaken_vs_ctx::date_hdr_time, ast_stir_shaken_vs_ctx::eprofile, verification_cfg_common::ignore_sip_date_header, LOG_ERROR, verification_cfg_common::max_date_header_age, SCOPE_ENTER, SCOPE_EXIT_LOG_RTN_VALUE, SCOPE_EXIT_RTN_VALUE, ast_stir_shaken_vs_ctx::tag, and profile_cfg::vcfg_common.
Referenced by ast_stir_shaken_vs_verify().
◆ check_tn_auth_list()
|
static |
Definition at line 254 of file verification.c.
References ASN1_TAG_TNAUTH_SPC, AST_STIR_SHAKEN_VS_CERT_NO_SPC_IN_TN_AUTH_EXT, AST_STIR_SHAKEN_VS_CERT_NO_TN_AUTH_EXT, AST_STIR_SHAKEN_VS_INTERNAL_ERROR, AST_STIR_SHAKEN_VS_SUCCESS, ast_string_field_set, ast_stir_shaken_vs_ctx::cert_cn, ast_stir_shaken_vs_ctx::cert_spc, crypto_get_cert_extension_data(), crypto_log_openssl(), get_tn_auth_nid(), IS_GET_OBJ_ERR, LOG_ERROR, NULL, ast_stir_shaken_vs_ctx::public_url, SCOPE_ENTER, SCOPE_EXIT_LOG_RTN_VALUE, SCOPE_EXIT_RTN_VALUE, ast_stir_shaken_vs_ctx::tag, and ast_stir_shaken_vs_ctx::xcert.
Referenced by check_cert().
◆ check_x5u_url()
|
static |
Definition at line 837 of file verification.c.
References AST_STIR_SHAKEN_VS_INVALID_OR_NO_X5U, ast_strings_equal(), ast_strlen_zero(), DUMP_X5U_MATCH, ast_stir_shaken_vs_ctx::eprofile, get_match_string, LOG_ERROR, verification_cfg_common::relax_x5u_path_restrictions, verification_cfg_common::relax_x5u_port_scheme_restrictions, SCOPE_ENTER, SCOPE_EXIT_LOG_RTN_VALUE, ast_stir_shaken_vs_ctx::tag, URL_MATCH_FRAGMENT, URL_MATCH_PORT, URL_MATCH_QUERY, url_match_regex, URL_MATCH_SCHEME, URL_MATCH_USERPASS, and profile_cfg::vcfg_common.
Referenced by ast_stir_shaken_vs_verify().
◆ cleanup_cert_from_astdb_and_fs()
|
static |
Definition at line 97 of file verification.c.
References ast_db_del(), ast_db_deltree(), ast_db_exists(), ast_stir_shaken_vs_ctx::filename, ast_stir_shaken_vs_ctx::hash_family, NULL, ast_stir_shaken_vs_ctx::public_url, remove, and ast_stir_shaken_vs_ctx::url_family.
Referenced by retrieve_cert_from_cache().
◆ ctx_destructor()
|
static |
Definition at line 647 of file verification.c.
References ao2_cleanup, ast_free, ast_string_field_free_memory, ast_stir_shaken_vs_ctx::eprofile, ast_stir_shaken_vs_ctx::raw_key, and ast_stir_shaken_vs_ctx::xcert.
Referenced by ast_stir_shaken_vs_ctx_create().
◆ ctx_populate()
|
static |
Definition at line 549 of file verification.c.
References AST_DB_FAMILY, ast_sha1_hash(), AST_STIR_SHAKEN_VS_INTERNAL_ERROR, AST_STIR_SHAKEN_VS_SUCCESS, ast_string_field_build, ast_string_field_set, verification_cfg_common::cert_cache_dir, ast_stir_shaken_vs_ctx::eprofile, ast_stir_shaken_vs_ctx::public_url, and profile_cfg::vcfg_common.
Referenced by ast_stir_shaken_vs_verify().
◆ is_cert_cache_entry_expired()
|
static |
Definition at line 225 of file verification.c.
References ast_str_to_ulong(), ast_strlen_zero(), ast_trace, ast_tvcmp(), ast_tvnow(), SCOPE_ENTER, and SCOPE_EXIT_RTN_VALUE.
Referenced by retrieve_cert_from_cache().
◆ retrieve_cert_from_cache()
|
static |
Definition at line 491 of file verification.c.
References ast_db_exists(), ast_db_get(), ast_file_is_readable(), AST_STIR_SHAKEN_VS_CERT_CACHE_EXPIRED, AST_STIR_SHAKEN_VS_CERT_CACHE_MISS, AST_STIR_SHAKEN_VS_CERT_CONTENTS_INVALID, AST_STIR_SHAKEN_VS_SUCCESS, check_cert(), cleanup_cert_from_astdb_and_fs(), crypto_load_cert_chain_from_file(), ast_stir_shaken_vs_ctx::expiration, ast_stir_shaken_vs_ctx::filename, ast_stir_shaken_vs_ctx::hash_family, is_cert_cache_entry_expired(), NULL, ast_stir_shaken_vs_ctx::public_url, SCOPE_ENTER, SCOPE_EXIT_RTN_VALUE, ast_stir_shaken_vs_ctx::tag, and ast_stir_shaken_vs_ctx::xcert.
Referenced by retrieve_verification_cert().
◆ retrieve_cert_from_url()
|
static |
Definition at line 378 of file verification.c.
References verification_cfg_common::acl, add_cert_key_to_astdb(), ast_begins_with(), ast_calloc, AST_STIR_SHAKEN_VS_CERT_CONTENTS_INVALID, AST_STIR_SHAKEN_VS_CERT_RETRIEVAL_FAILURE, AST_STIR_SHAKEN_VS_INTERNAL_ERROR, AST_STIR_SHAKEN_VS_SUCCESS, ast_strdup, ast_trace, ast_variable_find_in_list(), BEGIN_CERTIFICATE_STR, check_cert(), crypto_load_cert_chain_from_memory(), curl_header_data_free(), curl_open_socket_data_free(), verification_cfg_common::curl_timeout, curl_write_data_free(), curler(), ast_stir_shaken_vs_ctx::eprofile, errno, ast_stir_shaken_vs_ctx::filename, LOG_ERROR, NULL, ast_stir_shaken_vs_ctx::public_url, RAII_VAR, SCOPE_ENTER, SCOPE_EXIT_LOG_RTN_VALUE, SCOPE_EXIT_RTN_VALUE, ast_stir_shaken_vs_ctx::tag, profile_cfg::vcfg_common, and ast_stir_shaken_vs_ctx::xcert.
Referenced by retrieve_verification_cert().
◆ retrieve_verification_cert()
|
static |
Definition at line 577 of file verification.c.
References AST_STIR_SHAKEN_VS_SUCCESS, ast_trace, LOG_ERROR, ast_stir_shaken_vs_ctx::public_url, retrieve_cert_from_cache(), retrieve_cert_from_url(), SCOPE_ENTER, SCOPE_EXIT_LOG_RTN_VALUE, SCOPE_EXIT_RTN_VALUE, and ast_stir_shaken_vs_ctx::tag.
Referenced by ast_stir_shaken_vs_verify().
◆ vs_load()
| int vs_load | ( | void | ) |
Load the stir/shaken verification service.
- Return values
-
0 on success -1 on error
Definition at line 1122 of file verification.c.
References ast_log, AST_MODULE_LOAD_DECLINE, AST_MODULE_LOAD_SUCCESS, FULL_URL_REGEX, FULL_URL_REGEX_GROUPS, LOG_ERROR, url_match_regex, vs_config_load(), and vs_unload().
Referenced by common_config_load().
◆ vs_reload()
| int vs_reload | ( | void | ) |
Reload the stir/shaken verification service.
- Return values
-
0 on success -1 on error
Definition at line 1105 of file verification.c.
References vs_config_reload().
Referenced by common_config_reload().
◆ vs_response_code_to_str()
| const char * vs_response_code_to_str | ( | enum ast_stir_shaken_vs_response_code | vs_rc | ) |
Return string version of VS response code.
- Parameters
-
vs_rc
- Returns
- Response string
Definition at line 90 of file verification.c.
References ARRAY_IN_BOUNDS, NULL, and vs_rc_map.
Referenced by ast_stir_shaken_vs_verify(), and func_read_verification().
◆ vs_unload()
| int vs_unload | ( | void | ) |
Unload the stir/shaken verification service.
- Return values
-
0 on success -1 on error
Definition at line 1112 of file verification.c.
References url_match_regex, and vs_config_unload().
Referenced by common_config_unload(), and vs_load().
Variable Documentation
◆ url_match_regex
|
static |
Definition at line 48 of file verification.c.
Referenced by check_x5u_url(), vs_load(), and vs_unload().
◆ vs_rc_map
|
static |
Definition at line 53 of file verification.c.
Referenced by vs_response_code_to_str().