Secure RTP (SRTP) More...
#include "asterisk.h"#include <math.h>#include <srtp/srtp.h>#include <srtp/crypto_kernel.h>#include "asterisk/astobj2.h"#include "asterisk/frame.h"#include "asterisk/logger.h"#include "asterisk/module.h"#include "asterisk/sdp_srtp.h"#include "asterisk/res_srtp.h"#include "asterisk/rtp_engine.h"#include "asterisk/utils.h"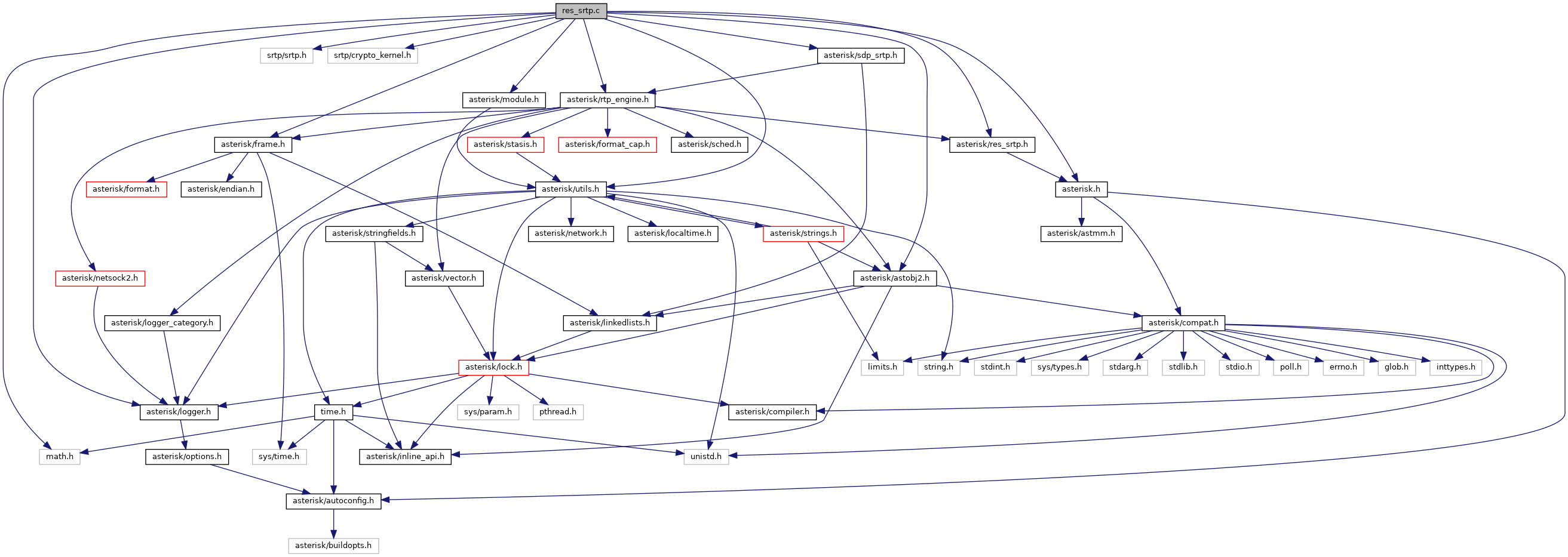
Go to the source code of this file.
Data Structures | |
| struct | ast_sdp_crypto |
| struct | ast_srtp |
| struct | ast_srtp_policy |
Functions | |
| static void | __reg_module (void) |
| static void | __unreg_module (void) |
| struct ast_module * | AST_MODULE_SELF_SYM (void) |
| static int | ast_srtp_add_stream (struct ast_srtp *srtp, struct ast_srtp_policy *policy) |
| static int | ast_srtp_change_source (struct ast_srtp *srtp, unsigned int from_ssrc, unsigned int to_ssrc) |
| static int | ast_srtp_create (struct ast_srtp **srtp, struct ast_rtp_instance *rtp, struct ast_srtp_policy *policy) |
| static void | ast_srtp_destroy (struct ast_srtp *srtp) |
| static int | ast_srtp_get_random (unsigned char *key, size_t len) |
| static struct ast_srtp_policy * | ast_srtp_policy_alloc (void) |
| static void | ast_srtp_policy_destroy (struct ast_srtp_policy *policy) |
| static int | ast_srtp_policy_set_master_key (struct ast_srtp_policy *policy, const unsigned char *key, size_t key_len, const unsigned char *salt, size_t salt_len) |
| static void | ast_srtp_policy_set_ssrc (struct ast_srtp_policy *policy, unsigned long ssrc, int inbound) |
| static int | ast_srtp_policy_set_suite (struct ast_srtp_policy *policy, enum ast_srtp_suite suite) |
| static int | ast_srtp_protect (struct ast_srtp *srtp, void **buf, int *len, int rtcp) |
| static int | ast_srtp_replace (struct ast_srtp **srtp, struct ast_rtp_instance *rtp, struct ast_srtp_policy *policy) |
| static void | ast_srtp_set_cb (struct ast_srtp *srtp, const struct ast_srtp_cb *cb, void *data) |
| static int | ast_srtp_unprotect (struct ast_srtp *srtp, void *buf, int *len, int rtcp) |
| static int | crypto_activate (struct ast_sdp_crypto *p, int suite_val, unsigned char *remote_key, int key_len, struct ast_rtp_instance *rtp) |
| static struct ast_sdp_crypto * | crypto_init_keys (struct ast_sdp_crypto *p, const int key_len) |
| static struct ast_srtp_policy * | find_policy (struct ast_srtp *srtp, const srtp_policy_t *policy, int flags) |
| static int | load_module (void) |
| static int | policy_cmp_fn (void *obj, void *arg, int flags) |
| static void | policy_destructor (void *obj) |
| static int | policy_hash_fn (const void *obj, const int flags) |
| static int | policy_set_suite (crypto_policy_t *p, enum ast_srtp_suite suite) |
| static struct ast_sdp_crypto * | res_sdp_crypto_alloc (void) |
| static int | res_sdp_crypto_build_offer (struct ast_sdp_crypto *p, int taglen) |
| static void | res_sdp_crypto_dtor (struct ast_sdp_crypto *crypto) |
| static int | res_sdp_crypto_parse_offer (struct ast_rtp_instance *rtp, struct ast_sdp_srtp *srtp, const char *attr) |
| static const char * | res_sdp_srtp_get_attr (struct ast_sdp_srtp *srtp, int dtls_enabled, int default_taglen_32) |
| static int | res_srtp_init (void) |
| static struct ast_srtp * | res_srtp_new (void) |
| static void | res_srtp_shutdown (void) |
| static struct ast_sdp_crypto * | sdp_crypto_alloc (const int key_len) |
| static int | set_crypto_policy (struct ast_srtp_policy *policy, int suite_val, const unsigned char *master_key, int key_len, unsigned long ssrc, int inbound) |
| static const char * | srtp_errstr (int err) |
| static void | srtp_event_cb (srtp_event_data_t *data) |
| static int | unload_module (void) |
Variables | |
| static struct ast_module_info | __mod_info = { .name = AST_MODULE, .flags = AST_MODFLAG_GLOBAL_SYMBOLS | AST_MODFLAG_LOAD_ORDER , .description = "Secure RTP (SRTP)" , .key = ASTERISK_GPL_KEY , .buildopt_sum = AST_BUILDOPT_SUM, .support_level = AST_MODULE_SUPPORT_CORE, .load = load_module, .unload = unload_module, .load_pri = AST_MODPRI_CHANNEL_DEPEND, } |
| static const struct ast_module_info * | ast_module_info = &__mod_info |
| static int | g_initialized = 0 |
| static struct ast_srtp_policy_res | policy_res |
| static struct ast_sdp_crypto_api | res_sdp_crypto_api |
| static struct ast_srtp_res | srtp_res |
Detailed Description
Function Documentation
◆ __reg_module()
|
static |
Definition at line 1312 of file res_srtp.c.
◆ __unreg_module()
|
static |
Definition at line 1312 of file res_srtp.c.
◆ AST_MODULE_SELF_SYM()
| struct ast_module * AST_MODULE_SELF_SYM | ( | void | ) |
Definition at line 1312 of file res_srtp.c.
◆ ast_srtp_add_stream()
|
static |
Definition at line 601 of file res_srtp.c.
References ao2_t_link, ao2_t_ref, ao2_t_unlink, ast_debug, ast_log, AST_LOG_WARNING, err_status_ok, find_policy(), match(), OBJ_POINTER, ast_srtp::policies, ast_srtp::session, and ast_srtp_policy::sp.
Referenced by ast_srtp_change_source().
◆ ast_srtp_change_source()
|
static |
Definition at line 635 of file res_srtp.c.
References ao2_t_ref, ast_debug, ast_log, ast_srtp_add_stream(), err_status_t, find_policy(), LOG_WARNING, match(), OBJ_POINTER, OBJ_UNLINK, ast_srtp::session, ast_srtp_policy::sp, and status.
◆ ast_srtp_create()
|
static |
Definition at line 542 of file res_srtp.c.
References ao2_t_link, ast_log, ast_module_ref, ast_srtp_destroy(), err_status_ok, LOG_ERROR, NULL, res_srtp_new(), ast_srtp::rtp, ast_module_info::self, ast_srtp::session, ast_srtp_policy::sp, srtp_errstr(), and status.
Referenced by ast_srtp_replace().
◆ ast_srtp_destroy()
|
static |
Definition at line 588 of file res_srtp.c.
References ao2_t_callback, ao2_t_ref, ast_free, ast_module_unref, NULL, OBJ_MULTIPLE, OBJ_NODATA, OBJ_UNLINK, ast_srtp::policies, ast_module_info::self, and ast_srtp::session.
Referenced by ast_srtp_create(), and ast_srtp_replace().
◆ ast_srtp_get_random()
|
static |
Definition at line 375 of file res_srtp.c.
References err_status_ok, and len().
◆ ast_srtp_policy_alloc()
|
static |
Definition at line 278 of file res_srtp.c.
References ao2_t_alloc, ast_log, LOG_ERROR, and policy_destructor().
◆ ast_srtp_policy_destroy()
|
static |
Definition at line 289 of file res_srtp.c.
References ao2_t_ref.
◆ ast_srtp_policy_set_master_key()
|
static |
Definition at line 353 of file res_srtp.c.
References ast_calloc, ast_free, NULL, and ast_srtp_policy::sp.
◆ ast_srtp_policy_set_ssrc()
|
static |
Definition at line 257 of file res_srtp.c.
References ast_srtp_policy::sp.
◆ ast_srtp_policy_set_suite()
|
static |
Definition at line 348 of file res_srtp.c.
References policy_set_suite(), and ast_srtp_policy::sp.
◆ ast_srtp_protect()
|
static |
Definition at line 514 of file res_srtp.c.
References ast_log, ast_srtp::buf, buf, err_status_ok, err_status_replay_fail, errno, len(), LOG_ERROR, LOG_WARNING, ast_srtp::rtcpbuf, ast_srtp::session, and srtp_errstr().
◆ ast_srtp_replace()
|
static |
Definition at line 571 of file res_srtp.c.
References ast_log, ast_srtp_create(), ast_srtp_destroy(), LOG_ERROR, and ast_srtp::rtp.
◆ ast_srtp_set_cb()
|
static |
Definition at line 384 of file res_srtp.c.
References ast_srtp::cb, and ast_srtp::data.
◆ ast_srtp_unprotect()
|
static |
Definition at line 395 of file res_srtp.c.
References ao2_container_count(), ao2_iterator_destroy(), ao2_iterator_init(), ao2_iterator_next, ao2_t_ref, ast_debug, ast_log, AST_LOG_NOTICE, ast_rtp_instance_get_ssrc(), ast_rtp_instance_get_stats(), AST_RTP_INSTANCE_STAT_REMOTE_SSRC, ast_verb, buf, ast_srtp::cb, ast_srtp::data, err_status_no_ctx, err_status_ok, err_status_replay_fail, err_status_replay_old, errno, len(), LOG_ERROR, ast_srtp_cb::no_ctx, NULL, ast_srtp::policies, ast_rtp_instance_stats::remote_ssrc, ast_srtp::rtp, ast_srtp::session, ast_srtp_policy::sp, srtp_errstr(), and ast_srtp::warned.
◆ crypto_activate()
|
static |
Definition at line 778 of file res_srtp.c.
References ast_srtp_policy_res::alloc, ast_debug, ast_log, ast_rtp_instance_add_srtp_policy(), ast_rtp_instance_get_stats(), AST_RTP_INSTANCE_STAT_LOCAL_SSRC, ast_srtp_policy_res::destroy, ast_sdp_crypto::local_key, ast_rtp_instance_stats::local_ssrc, LOG_WARNING, NULL, policy_res, and set_crypto_policy().
Referenced by res_sdp_crypto_parse_offer().
◆ crypto_init_keys()
|
static |
Definition at line 680 of file res_srtp.c.
References ast_base64decode(), ast_base64encode(), ast_debug, ast_log, ast_srtp_res::get_random, ast_sdp_crypto::key_len, ast_sdp_crypto::local_key, ast_sdp_crypto::local_key64, LOG_ERROR, NULL, ast_sdp_crypto::remote_key, and srtp_res.
Referenced by res_sdp_crypto_parse_offer(), and sdp_crypto_alloc().
◆ find_policy()
|
static |
Definition at line 203 of file res_srtp.c.
References ao2_t_find, ast_srtp::policies, and ast_srtp_policy::sp.
Referenced by ast_srtp_add_stream(), and ast_srtp_change_source().
◆ load_module()
|
static |
◆ policy_cmp_fn()
|
static |
Definition at line 196 of file res_srtp.c.
References ast_srtp_policy::sp.
Referenced by res_srtp_new().
◆ policy_destructor()
|
static |
Definition at line 268 of file res_srtp.c.
References ast_free, NULL, and ast_srtp_policy::sp.
Referenced by ast_srtp_policy_alloc().
◆ policy_hash_fn()
|
static |
Definition at line 189 of file res_srtp.c.
References ast_srtp_policy::sp.
Referenced by res_srtp_new().
◆ policy_set_suite()
|
static |
Definition at line 294 of file res_srtp.c.
References AST_AES_CM_128_HMAC_SHA1_32, AST_AES_CM_128_HMAC_SHA1_80, AST_AES_CM_192_HMAC_SHA1_32, AST_AES_CM_192_HMAC_SHA1_80, AST_AES_CM_256_HMAC_SHA1_32, AST_AES_CM_256_HMAC_SHA1_80, AST_AES_GCM_128, AST_AES_GCM_128_8, AST_AES_GCM_256, AST_AES_GCM_256_8, ast_log, crypto_policy_set_aes_cm_128_hmac_sha1_32, crypto_policy_set_aes_cm_128_hmac_sha1_80, crypto_policy_set_aes_cm_192_hmac_sha1_32, crypto_policy_set_aes_cm_192_hmac_sha1_80, crypto_policy_set_aes_cm_256_hmac_sha1_32, crypto_policy_set_aes_cm_256_hmac_sha1_80, crypto_policy_set_aes_gcm_128_16_auth, crypto_policy_set_aes_gcm_128_8_auth, crypto_policy_set_aes_gcm_256_16_auth, crypto_policy_set_aes_gcm_256_8_auth, and LOG_ERROR.
Referenced by ast_srtp_policy_set_suite().
◆ res_sdp_crypto_alloc()
|
static |
Definition at line 726 of file res_srtp.c.
References sdp_crypto_alloc(), and SRTP_MASTER_KEY_LEN.
Referenced by res_sdp_srtp_get_attr().
◆ res_sdp_crypto_build_offer()
|
static |
Definition at line 731 of file res_srtp.c.
References ast_sdp_crypto::a_crypto, ast_asprintf, ast_debug, ast_free, ast_log, ast_sdp_crypto::local_key64, LOG_ERROR, NULL, and ast_sdp_crypto::tag.
Referenced by res_sdp_crypto_parse_offer(), and res_sdp_srtp_get_attr().
◆ res_sdp_crypto_dtor()
|
static |
Definition at line 669 of file res_srtp.c.
References ast_sdp_crypto::a_crypto, ast_free, ast_module_unref, NULL, and ast_module_info::self.
Referenced by sdp_crypto_alloc().
◆ res_sdp_crypto_parse_offer()
|
static |
Definition at line 830 of file res_srtp.c.
References AES_128_GCM_KEYSIZE_WSALT, AES_256_GCM_KEYSIZE_WSALT, AST_AES_CM_128_HMAC_SHA1_32, AST_AES_CM_128_HMAC_SHA1_80, AST_AES_CM_192_HMAC_SHA1_32, AST_AES_CM_192_HMAC_SHA1_80, AST_AES_CM_256_HMAC_SHA1_32, AST_AES_CM_256_HMAC_SHA1_80, AST_AES_GCM_128, AST_AES_GCM_128_8, AST_AES_GCM_256, AST_AES_GCM_256_8, ast_base64decode(), ast_clear_flag, ast_debug, AST_LIST_NEXT, ast_log, ast_set_flag, AST_SRTP_CRYPTO_AES_192, AST_SRTP_CRYPTO_AES_256, AST_SRTP_CRYPTO_OFFER_OK, AST_SRTP_CRYPTO_OLD_NAME, AST_SRTP_CRYPTO_TAG_16, AST_SRTP_CRYPTO_TAG_32, AST_SRTP_CRYPTO_TAG_8, AST_SRTP_CRYPTO_TAG_80, ast_strdupa, ast_strlen_zero(), ast_test_flag, ast_sdp_srtp::crypto, crypto_activate(), crypto_init_keys(), ast_sdp_srtp::flags, ast_sdp_crypto::key_len, LOG_ERROR, LOG_NOTICE, LOG_WARNING, method, NULL, ast_sdp_crypto::remote_key, res_sdp_crypto_build_offer(), ast_sdp_srtp::sdp_srtp_list, str, strsep(), and ast_sdp_crypto::tag.
◆ res_sdp_srtp_get_attr()
|
static |
Definition at line 1127 of file res_srtp.c.
References ast_sdp_crypto::a_crypto, AES_128_GCM_KEYSIZE_WSALT, AES_256_GCM_KEYSIZE_WSALT, ARRAY_LEN, AST_LIST_NEXT, ast_log, ast_sdp_srtp_alloc(), ast_set_flag, AST_SRTP_CRYPTO_AES_192, AST_SRTP_CRYPTO_AES_256, AST_SRTP_CRYPTO_OLD_NAME, AST_SRTP_CRYPTO_TAG_16, AST_SRTP_CRYPTO_TAG_32, AST_SRTP_CRYPTO_TAG_8, AST_SRTP_CRYPTO_TAG_80, ast_test_flag, ast_sdp_srtp::crypto, len(), LOG_ERROR, LOG_WARNING, NULL, res_sdp_crypto_alloc(), res_sdp_crypto_build_offer(), sdp_crypto_alloc(), ast_sdp_srtp::sdp_srtp_list, and ast_sdp_crypto::tag.
◆ res_srtp_init()
|
static |
Definition at line 1257 of file res_srtp.c.
References ast_log, AST_LOG_WARNING, ast_rtp_engine_register_srtp(), ast_sdp_crypto_register(), ast_verb, err_status_ok, g_initialized, policy_res, res_sdp_crypto_api, res_srtp_shutdown(), srtp_event_cb(), and srtp_res.
Referenced by load_module().
◆ res_srtp_new()
|
static |
Definition at line 215 of file res_srtp.c.
References AO2_ALLOC_OPT_LOCK_MUTEX, ao2_t_container_alloc_hash, ast_calloc, ast_free, ast_log, LOG_ERROR, NULL, ast_srtp::policies, policy_cmp_fn(), policy_hash_fn(), and ast_srtp::warned.
Referenced by ast_srtp_create().
◆ res_srtp_shutdown()
|
static |
Definition at line 1246 of file res_srtp.c.
References ast_rtp_engine_unregister_srtp(), ast_sdp_crypto_unregister(), g_initialized, NULL, and res_sdp_crypto_api.
Referenced by res_srtp_init(), and unload_module().
◆ sdp_crypto_alloc()
|
static |
Definition at line 707 of file res_srtp.c.
References ast_calloc, ast_module_ref, crypto_init_keys(), ast_sdp_crypto::key_len, NULL, res_sdp_crypto_dtor(), result, ast_module_info::self, and ast_sdp_crypto::tag.
Referenced by res_sdp_crypto_alloc(), and res_sdp_srtp_get_attr().
◆ set_crypto_policy()
|
static |
Definition at line 762 of file res_srtp.c.
References ast_log, ast_sdp_crypto::key_len, LOG_WARNING, NULL, policy_res, ast_srtp_policy_res::set_master_key, ast_srtp_policy_res::set_ssrc, and ast_srtp_policy_res::set_suite.
Referenced by crypto_activate().
◆ srtp_errstr()
|
static |
Definition at line 149 of file res_srtp.c.
References err_status_algo_fail, err_status_alloc_fail, err_status_auth_fail, err_status_bad_param, err_status_cant_check, err_status_cipher_fail, err_status_dealloc_fail, err_status_fail, err_status_init_fail, err_status_key_expired, err_status_no_ctx, err_status_no_such_op, err_status_ok, err_status_replay_fail, err_status_replay_old, and err_status_terminus.
Referenced by ast_srtp_create(), ast_srtp_protect(), and ast_srtp_unprotect().
◆ srtp_event_cb()
|
static |
Definition at line 239 of file res_srtp.c.
References ast_debug, and ast_srtp::data.
Referenced by res_srtp_init().
◆ unload_module()
|
static |
Definition at line 1301 of file res_srtp.c.
References res_srtp_shutdown().
Variable Documentation
◆ __mod_info
|
static |
Definition at line 1312 of file res_srtp.c.
◆ ast_module_info
|
static |
Definition at line 1312 of file res_srtp.c.
◆ g_initialized
|
static |
Tracks whether or not we've initialized the libsrtp library
Definition at line 108 of file res_srtp.c.
Referenced by res_srtp_init(), and res_srtp_shutdown().
◆ policy_res
|
static |
Definition at line 141 of file res_srtp.c.
Referenced by ast_rtp_engine_register_srtp(), crypto_activate(), res_srtp_init(), and set_crypto_policy().
◆ res_sdp_crypto_api
|
static |
Definition at line 1238 of file res_srtp.c.
Referenced by res_srtp_init(), and res_srtp_shutdown().
◆ srtp_res
|
static |
Definition at line 129 of file res_srtp.c.
Referenced by ast_rtp_engine_register_srtp(), crypto_init_keys(), and res_srtp_init().