Provide Cryptographic Signature capability. More...
#include "asterisk.h"#include <dirent.h>#include <sys/stat.h>#include <openssl/err.h>#include <openssl/ssl.h>#include <openssl/evp.h>#include <openssl/md5.h>#include <openssl/sha.h>#include "asterisk/cli.h"#include "asterisk/compat.h"#include "asterisk/io.h"#include "asterisk/linkedlists.h"#include "asterisk/logger.h"#include "asterisk/md5.h"#include "asterisk/module.h"#include "asterisk/options.h"#include "asterisk/paths.h"#include "asterisk/utils.h"#include "asterisk/file.h"#include "asterisk/crypto.h"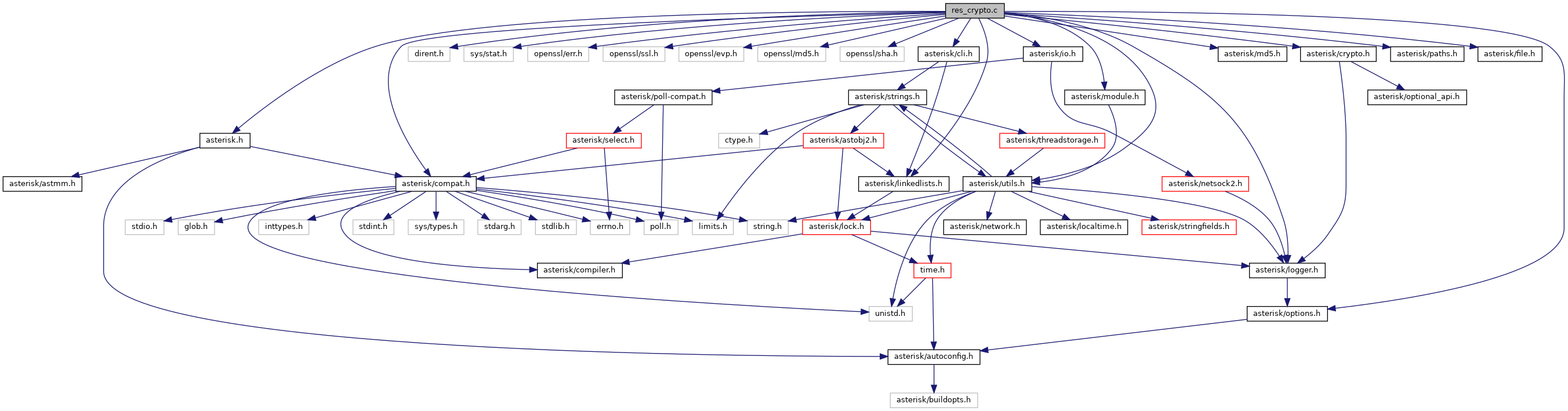
Go to the source code of this file.
Data Structures | |
| struct | ast_key |
| struct | crypto_load_on_file |
| struct | keys |
Macros | |
| #define | AST_API_MODULE |
| #define | FILE_MODE_BITS (S_ISUID|S_ISGID|S_ISVTX|S_IRWXU|S_IRWXG|S_IRWXO) |
| #define | FORMAT "%-18s %-8s %-16s %-33s\n" |
| #define | KEY_NEEDS_PASSCODE (1 << 16) |
| #define | RSA_PKCS1_OAEP_PADDING_SIZE (1 + 2 * SHA_DIGEST_LENGTH) |
Functions | |
| static void | __reg_module (void) |
| static void | __unreg_module (void) |
| int AST_OPTIONAL_API_NAME() | ast_aes_decrypt (const unsigned char *in, unsigned char *out, const ast_aes_decrypt_key *key) |
| AES decrypt data. | |
| int AST_OPTIONAL_API_NAME() | ast_aes_encrypt (const unsigned char *in, unsigned char *out, const ast_aes_encrypt_key *key) |
| AES encrypt data. | |
| int AST_OPTIONAL_API_NAME() | ast_aes_set_decrypt_key (const unsigned char *key, ast_aes_decrypt_key *ctx) |
| Set a decryption key. | |
| int AST_OPTIONAL_API_NAME() | ast_aes_set_encrypt_key (const unsigned char *key, ast_aes_encrypt_key *ctx) |
| Set an encryption key. | |
| int AST_OPTIONAL_API_NAME() | ast_check_signature (struct ast_key *key, const char *msg, const char *sig) |
| base64 decode then sent to __ast_check_signature_bin | |
| int AST_OPTIONAL_API_NAME() | ast_check_signature_bin (struct ast_key *key, const char *msg, int msglen, const unsigned char *dsig) |
| check signature of a message | |
| int AST_OPTIONAL_API_NAME() | ast_crypto_loaded (void) |
| int AST_OPTIONAL_API_NAME() | ast_crypto_reload (void) |
| int AST_OPTIONAL_API_NAME() | ast_decrypt_bin (unsigned char *dst, const unsigned char *src, int srclen, struct ast_key *key) |
| decrypt a message | |
| int AST_OPTIONAL_API_NAME() | ast_encrypt_bin (unsigned char *dst, const unsigned char *src, int srclen, struct ast_key *key) |
| encrypt a message | |
| struct ast_key *AST_OPTIONAL_API_NAME() | ast_key_get (const char *kname, int ktype) |
| return the ast_key structure for name | |
| struct ast_module * | AST_MODULE_SELF_SYM (void) |
| int AST_OPTIONAL_API_NAME() | ast_sign (struct ast_key *key, char *msg, char *sig) |
| wrapper for __ast_sign_bin then base64 encode it | |
| int AST_OPTIONAL_API_NAME() | ast_sign_bin (struct ast_key *key, const char *msg, int msglen, unsigned char *dsig) |
| signs outgoing message with public key | |
| static int | crypto_init (void) |
| initialise the res_crypto module | |
| static void | crypto_load (int ifd, int ofd) |
| refresh RSA keys from file | |
| static int | crypto_load_cb (const char *directory, const char *file, void *obj) |
| static int | evp_cipher_aes_decrypt (const unsigned char *in, unsigned char *out, unsigned inlen, const ast_aes_decrypt_key *key) |
| static int | evp_cipher_aes_encrypt (const unsigned char *in, unsigned char *out, unsigned inlen, const ast_aes_encrypt_key *key) |
| static int | evp_pkey_decrypt (EVP_PKEY *pkey, const unsigned char *in, unsigned inlen, unsigned char *out, unsigned *outlen, unsigned padding) |
| static int | evp_pkey_encrypt (EVP_PKEY *pkey, const unsigned char *in, unsigned inlen, unsigned char *out, unsigned *outlen, unsigned padding) |
| static int | evp_pkey_sign (EVP_PKEY *pkey, const unsigned char *in, unsigned inlen, unsigned char *sig, unsigned *siglen, unsigned padding) |
| static int | evp_pkey_verify (EVP_PKEY *pkey, const unsigned char *in, unsigned inlen, const unsigned char *sig, unsigned siglen, unsigned padding) |
| static char * | handle_cli_keys_init (struct ast_cli_entry *e, int cmd, struct ast_cli_args *a) |
| initialize all RSA keys | |
| static char * | handle_cli_keys_show (struct ast_cli_entry *e, int cmd, struct ast_cli_args *a) |
| show the list of RSA keys | |
| static int | load_module (void) |
| static void | md52sum (char *sum, unsigned char *md5) |
| static int | pw_cb (char *buf, int size, int rwflag, void *userdata) |
| setting of priv key | |
| static int | reload (void) |
| static struct ast_key * | try_load_key (const char *dir, const char *fname, int ifd, int ofd, int *not2) |
| load RSA key from file | |
| static int | unload_module (void) |
Variables | |
| static struct ast_module_info | __mod_info = { .name = AST_MODULE, .flags = AST_MODFLAG_GLOBAL_SYMBOLS | AST_MODFLAG_LOAD_ORDER , .description = "Cryptographic Digital Signatures" , .key = ASTERISK_GPL_KEY , .buildopt_sum = AST_BUILDOPT_SUM, .support_level = AST_MODULE_SUPPORT_CORE, .load = load_module, .unload = unload_module, .reload = reload, .load_pri = AST_MODPRI_CHANNEL_DEPEND, } |
| static const struct ast_module_info * | ast_module_info = &__mod_info |
| static struct ast_cli_entry | cli_crypto [] |
| static struct keys | keys = AST_RWLIST_HEAD_INIT_VALUE |
Detailed Description
Provide Cryptographic Signature capability.
Uses the OpenSSL library, available at http://www.openssl.org/
Definition in file res_crypto.c.
Macro Definition Documentation
◆ AST_API_MODULE
| #define AST_API_MODULE |
Definition at line 57 of file res_crypto.c.
◆ FILE_MODE_BITS
| #define FILE_MODE_BITS (S_ISUID|S_ISGID|S_ISVTX|S_IRWXU|S_IRWXG|S_IRWXO) |
◆ FORMAT
| #define FORMAT "%-18s %-8s %-16s %-33s\n" |
◆ KEY_NEEDS_PASSCODE
| #define KEY_NEEDS_PASSCODE (1 << 16) |
Definition at line 73 of file res_crypto.c.
◆ RSA_PKCS1_OAEP_PADDING_SIZE
| #define RSA_PKCS1_OAEP_PADDING_SIZE (1 + 2 * SHA_DIGEST_LENGTH) |
Definition at line 78 of file res_crypto.c.
Function Documentation
◆ __reg_module()
|
static |
Definition at line 996 of file res_crypto.c.
◆ __unreg_module()
|
static |
Definition at line 996 of file res_crypto.c.
◆ ast_aes_decrypt()
| int AST_OPTIONAL_API_NAME() ast_aes_decrypt | ( | const unsigned char * | in, |
| unsigned char * | out, | ||
| const ast_aes_decrypt_key * | key | ||
| ) |
AES decrypt data.
- Parameters
-
in encrypted data out pointer to a buffer to hold the decrypted output key pointer to the ast_aes_decrypt_key to use for decryption
- Return values
-
<= 0 failure otherwise number of bytes in output buffer
Definition at line 790 of file res_crypto.c.
References AST_CRYPTO_AES_BLOCKSIZE, ast_log, evp_cipher_aes_decrypt(), in, LOG_ERROR, and out.
Referenced by aes_helper(), AST_TEST_DEFINE(), decrypt_memcpy(), and memcpy_decrypt().
◆ ast_aes_encrypt()
| int AST_OPTIONAL_API_NAME() ast_aes_encrypt | ( | const unsigned char * | in, |
| unsigned char * | out, | ||
| const ast_aes_encrypt_key * | key | ||
| ) |
AES encrypt data.
- Parameters
-
in data to be encrypted out pointer to a buffer to hold the encrypted output key pointer to the ast_aes_encrypt_key to use for encryption
- Return values
-
<= 0 failure otherwise number of bytes in output buffer
Definition at line 749 of file res_crypto.c.
References AST_CRYPTO_AES_BLOCKSIZE, ast_log, evp_cipher_aes_encrypt(), in, LOG_ERROR, and out.
Referenced by aes_helper(), AST_TEST_DEFINE(), encrypt_memcpy(), and memcpy_encrypt().
◆ ast_aes_set_decrypt_key()
| int AST_OPTIONAL_API_NAME() ast_aes_set_decrypt_key | ( | const unsigned char * | key, |
| ast_aes_decrypt_key * | ctx | ||
| ) |
Set a decryption key.
- Parameters
-
key a 16 char key ctx address of an aes encryption context
- Return values
-
0 success nonzero failure
Definition at line 709 of file res_crypto.c.
References AST_CRYPTO_AES_BLOCKSIZE, and NULL.
Referenced by aes_helper(), AST_TEST_DEFINE(), build_ecx_key(), build_encryption_keys(), check_key(), socket_process_helper(), and update_key().
◆ ast_aes_set_encrypt_key()
| int AST_OPTIONAL_API_NAME() ast_aes_set_encrypt_key | ( | const unsigned char * | key, |
| ast_aes_encrypt_key * | ctx | ||
| ) |
Set an encryption key.
- Parameters
-
key a 16 char key ctx address of an aes encryption context
- Return values
-
0 success nonzero failure
Definition at line 700 of file res_crypto.c.
References AST_CRYPTO_AES_BLOCKSIZE, and NULL.
Referenced by aes_helper(), AST_TEST_DEFINE(), build_ecx_key(), check_key(), and update_key().
◆ ast_check_signature()
| int AST_OPTIONAL_API_NAME() ast_check_signature | ( | struct ast_key * | key, |
| const char * | msg, | ||
| const char * | sig | ||
| ) |
base64 decode then sent to __ast_check_signature_bin
Check the authenticity of a message signature using a given public key.
- See also
- ast_check_signature
Definition at line 673 of file res_crypto.c.
References ast_base64decode(), ast_check_signature_bin(), ast_log, and LOG_WARNING.
Referenced by authenticate_verify(), and register_verify().
◆ ast_check_signature_bin()
| int AST_OPTIONAL_API_NAME() ast_check_signature_bin | ( | struct ast_key * | key, |
| const char * | msg, | ||
| int | msglen, | ||
| const unsigned char * | dsig | ||
| ) |
check signature of a message
Check the authenticity of a message signature using a given public key.
- See also
- ast_check_signature_bin
Definition at line 634 of file res_crypto.c.
References ast_debug, AST_KEY_PUBLIC, ast_log, ast_key::digest, evp_pkey_verify(), ast_key::ktype, LOG_ERROR, LOG_WARNING, ast_key::name, NULL, and ast_key::pkey.
Referenced by ast_check_signature(), AST_TEST_DEFINE(), and check_key().
◆ ast_crypto_loaded()
| int AST_OPTIONAL_API_NAME() ast_crypto_loaded | ( | void | ) |
Definition at line 689 of file res_crypto.c.
Referenced by AST_TEST_DEFINE().
◆ ast_crypto_reload()
| int AST_OPTIONAL_API_NAME() ast_crypto_reload | ( | void | ) |
Definition at line 694 of file res_crypto.c.
References crypto_load().
Referenced by AST_TEST_DEFINE(), AST_TEST_DEFINE(), AST_TEST_DEFINE(), and AST_TEST_DEFINE().
◆ ast_decrypt_bin()
| int AST_OPTIONAL_API_NAME() ast_decrypt_bin | ( | unsigned char * | dst, |
| const unsigned char * | src, | ||
| int | srclen, | ||
| struct ast_key * | key | ||
| ) |
decrypt a message
Decrypt a message using a given private key.
- See also
- ast_decrypt_bin
Definition at line 472 of file res_crypto.c.
References AST_KEY_PRIVATE, ast_log, evp_pkey_decrypt(), ast_key::ktype, LOG_NOTICE, LOG_WARNING, and ast_key::pkey.
Referenced by AST_TEST_DEFINE(), and check_key().
◆ ast_encrypt_bin()
| int AST_OPTIONAL_API_NAME() ast_encrypt_bin | ( | unsigned char * | dst, |
| const unsigned char * | src, | ||
| int | srclen, | ||
| struct ast_key * | key | ||
| ) |
encrypt a message
Encrypt a message using a given private key.
- See also
- ast_encrypt_bin
Definition at line 549 of file res_crypto.c.
References AST_KEY_PUBLIC, ast_log, evp_pkey_encrypt(), ast_key::ktype, LOG_NOTICE, LOG_WARNING, ast_key::pkey, and RSA_PKCS1_OAEP_PADDING_SIZE.
Referenced by AST_TEST_DEFINE(), and update_key().
◆ ast_key_get()
| struct ast_key *AST_OPTIONAL_API_NAME() ast_key_get | ( | const char * | kname, |
| int | ktype | ||
| ) |
return the ast_key structure for name
Retrieve a key.
- See also
- ast_key_get
Definition at line 149 of file res_crypto.c.
References AST_RWLIST_RDLOCK, AST_RWLIST_TRAVERSE, AST_RWLIST_UNLOCK, ast_key::ktype, ast_key::list, and ast_key::name.
Referenced by AST_TEST_DEFINE(), AST_TEST_DEFINE(), AST_TEST_DEFINE(), AST_TEST_DEFINE(), authenticate(), authenticate_verify(), check_key(), register_verify(), and update_key().
◆ AST_MODULE_SELF_SYM()
| struct ast_module * AST_MODULE_SELF_SYM | ( | void | ) |
Definition at line 996 of file res_crypto.c.
◆ ast_sign()
| int AST_OPTIONAL_API_NAME() ast_sign | ( | struct ast_key * | key, |
| char * | msg, | ||
| char * | sig | ||
| ) |
wrapper for __ast_sign_bin then base64 encode it
Sign a message signature using a given private key.
- See also
- ast_sign
Definition at line 584 of file res_crypto.c.
References ast_base64encode(), and ast_sign_bin().
Referenced by authenticate().
◆ ast_sign_bin()
| int AST_OPTIONAL_API_NAME() ast_sign_bin | ( | struct ast_key * | key, |
| const char * | msg, | ||
| int | msglen, | ||
| unsigned char * | dsig | ||
| ) |
signs outgoing message with public key
Sign a message signature using a given private key.
- See also
- ast_sign_bin
Definition at line 390 of file res_crypto.c.
References AST_KEY_PRIVATE, ast_log, ast_key::digest, evp_pkey_sign(), ast_key::ktype, LOG_ERROR, LOG_WARNING, ast_key::name, NULL, and ast_key::pkey.
Referenced by ast_sign(), AST_TEST_DEFINE(), and update_key().
◆ crypto_init()
|
static |
initialise the res_crypto module
Definition at line 959 of file res_crypto.c.
References ARRAY_LEN, ast_cli_register_multiple, and cli_crypto.
Referenced by load_module().
◆ crypto_load()
|
static |
refresh RSA keys from file
- Parameters
-
ifd file descriptor ofd file descriptor
Definition at line 819 of file res_crypto.c.
References ast_config_AST_KEY_DIR, ast_debug, ast_file_read_dirs(), ast_free, ast_log, AST_RWLIST_REMOVE_CURRENT, AST_RWLIST_TRAVERSE, AST_RWLIST_TRAVERSE_SAFE_BEGIN, AST_RWLIST_TRAVERSE_SAFE_END, AST_RWLIST_UNLOCK, AST_RWLIST_WRLOCK, crypto_load_cb(), ast_key::delme, crypto_load_on_file::ifd, ast_key::ktype, LOG_NOTICE, LOG_WARNING, ast_key::name, crypto_load_on_file::note, crypto_load_on_file::ofd, and ast_key::pkey.
◆ crypto_load_cb()
|
static |
Definition at line 806 of file res_crypto.c.
References crypto_load_on_file::ifd, crypto_load_on_file::note, crypto_load_on_file::ofd, and try_load_key().
Referenced by crypto_load().
◆ evp_cipher_aes_decrypt()
|
static |
Definition at line 759 of file res_crypto.c.
References AST_CRYPTO_AES_BLOCKSIZE, in, NULL, out, and aes_key::raw.
Referenced by ast_aes_decrypt().
◆ evp_cipher_aes_encrypt()
|
static |
Definition at line 718 of file res_crypto.c.
References AST_CRYPTO_AES_BLOCKSIZE, in, NULL, out, and aes_key::raw.
Referenced by ast_aes_encrypt().
◆ evp_pkey_decrypt()
|
static |
Definition at line 432 of file res_crypto.c.
References in, NULL, out, and ast_key::pkey.
Referenced by ast_decrypt_bin().
◆ evp_pkey_encrypt()
|
static |
Definition at line 504 of file res_crypto.c.
References ast_log, in, LOG_WARNING, NULL, out, ast_key::pkey, and RSA_PKCS1_OAEP_PADDING_SIZE.
Referenced by ast_encrypt_bin().
◆ evp_pkey_sign()
|
static |
Definition at line 351 of file res_crypto.c.
Referenced by ast_sign_bin().
◆ evp_pkey_verify()
|
static |
Definition at line 598 of file res_crypto.c.
References in, NULL, and ast_key::pkey.
Referenced by ast_check_signature_bin().
◆ handle_cli_keys_init()
|
static |
initialize all RSA keys
- Parameters
-
e CLI command cmd a list of CLI arguments
- Return values
-
CLI_SUCCESS
Definition at line 916 of file res_crypto.c.
References a, ast_config_AST_KEY_DIR, ast_copy_string(), AST_RWLIST_TRAVERSE_SAFE_BEGIN, AST_RWLIST_TRAVERSE_SAFE_END, AST_RWLIST_UNLOCK, AST_RWLIST_WRLOCK, CLI_GENERATE, CLI_INIT, CLI_SHOWUSAGE, CLI_SUCCESS, ast_cli_entry::command, ast_key::fn, KEY_NEEDS_PASSCODE, ast_key::ktype, ast_key::list, NULL, try_load_key(), and ast_cli_entry::usage.
◆ handle_cli_keys_show()
|
static |
show the list of RSA keys
- Parameters
-
e CLI command cmd a list of CLI arguments
- Return values
-
CLI_SUCCESS
Definition at line 870 of file res_crypto.c.
References a, ast_cli(), AST_KEY_PUBLIC, AST_RWLIST_RDLOCK, AST_RWLIST_TRAVERSE, AST_RWLIST_UNLOCK, CLI_GENERATE, CLI_INIT, CLI_SUCCESS, ast_cli_entry::command, ast_key::digest, FORMAT, KEY_NEEDS_PASSCODE, ast_key::ktype, ast_key::list, md52sum(), MD5_DIGEST_LENGTH, ast_key::name, NULL, and ast_cli_entry::usage.
◆ load_module()
|
static |
Definition at line 971 of file res_crypto.c.
References AST_MODULE_LOAD_SUCCESS, ast_opt_init_keys, crypto_init(), and crypto_load().
◆ md52sum()
|
static |
Definition at line 855 of file res_crypto.c.
References md5(), and MD5_DIGEST_LENGTH.
Referenced by handle_cli_keys_show().
◆ pw_cb()
|
static |
setting of priv key
- Parameters
-
buf size rwflag userdata
- Returns
- length of string,-1 on failure
Definition at line 112 of file res_crypto.c.
References ast_hide_password(), AST_KEY_PRIVATE, ast_log, ast_restore_tty(), buf, errno, ast_key::infd, ast_key::ktype, LOG_WARNING, ast_key::name, ast_key::outfd, and prompt.
Referenced by try_load_key().
◆ reload()
|
static |
Definition at line 965 of file res_crypto.c.
References crypto_load().
◆ try_load_key()
|
static |
load RSA key from file
- Parameters
-
dir directory string fname name of file ifd incoming file descriptor ofd outgoing file descriptor not2
- Returns
- key on success.
- Return values
-
NULL on failure.
Definition at line 175 of file res_crypto.c.
References ast_calloc, ast_copy_string(), AST_CRYPTO_RSA_KEY_BITS, ast_debug, AST_KEY_PRIVATE, AST_KEY_PUBLIC, ast_log, ast_opt_init_keys, AST_RWLIST_INSERT_TAIL, AST_RWLIST_TRAVERSE, ast_verb, buf, c, ast_key::delme, ast_key::digest, errno, FILE_MODE_BITS, ast_key::fn, ast_key::infd, KEY_NEEDS_PASSCODE, ast_key::ktype, LOG_ERROR, LOG_NOTICE, LOG_WARNING, MD5_DIGEST_LENGTH, ast_key::name, NULL, ast_key::outfd, ast_key::pkey, and pw_cb().
Referenced by crypto_load_cb(), and handle_cli_keys_init().
◆ unload_module()
|
static |
Since we don't have a config file, we could move up to REALTIME_DEPEND, if necessary
Definition at line 983 of file res_crypto.c.
References ARRAY_LEN, ast_cli_unregister_multiple(), and cli_crypto.
Variable Documentation
◆ __mod_info
|
static |
Definition at line 996 of file res_crypto.c.
◆ ast_module_info
|
static |
Definition at line 996 of file res_crypto.c.
◆ cli_crypto
|
static |
Definition at line 953 of file res_crypto.c.
Referenced by crypto_init(), and unload_module().
◆ keys
|
static |